Just like a lot of other Rhythmbox users I like to scrobble my played tracks to last.fm. Unfortunately Rhythmbox provides no way to love a track. The last.fm plug-ins for Windows and OS X have been modified to scrobble through the last.fm client some time ago but the Rhythmbox plug-in still submits directly. That is until now…
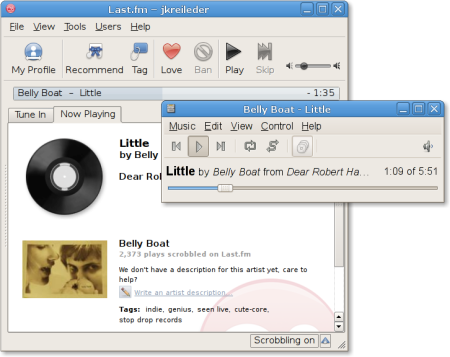
I have written a new last.fm plug-in for Rhythmbox today. Instead of scrobbling directly like the old one, it submits tracks via the lastfm client application. The client displays additional information about the currently playing song and you can love and tag the song with it.
The source code is available as a patch against Rhythmbox 2.90.1 (git snapshot 20120108): scrobbler-v3t.patch
You can apply this patch with:
patch -NEp1 < ~/scrobbler-v3t.patch
Ubuntu Oneiric Ocelot users can get precompiled packages from my APT repositories by running these commands in a terminal:
$ sudo add-apt-repository \
'/static/debian/rhythmbox/ main'
$ wget /static/gpg.asc -O - | \
sudo apt-key add -
$ sudo apt-get update
$ sudo apt-get install rhythmbox rhythmbox-plugins lastfm
To enable the new plug-in go to Edit » Plugins. Disable the “Last.fm” plug-in and enable the “New Style Last.fm Scrobbler”.
If you enable this scrobbler plug-in, you have to disable the old Last.fm plug-in! Otherwise you will have two plug-ins which will both submit to last.fm at the same time. Only use one at a time!
Note that this first version of the plug-in does not start the lastfm client automatically! It will scrobble only if you start the client manually. I will fix this in the next version.
Feedback, postive as well as negative, is very welcome. If you want to report a bug, please include the output of “rhythmbox -D rb-scrobbler-plugin” and the tags of the song you wanted to scrobble.
If you want to report a crash, providing a gdb backtrace would be nice.
You might also want to take a look at this thread on the last.fm development forum.
May 20th, 2007: v2 of the plug-in is available now. lastfm gets launched automatically now.
May 22nd, 2007: v3 is available. The patch and the Ubuntu package have been updated: Changes since v2
May 25th, 2007: v3a: Updated patch and deb for the new Ubuntu Gutsy version of Rhythmbox.
May 29th, 2007: v3b: Updated patch and deb for the new Rhythmbox release.
May 31st, 2007: Updated patch Ubuntu package.
June 1st, 2007: Added APT repositories for Ubuntu Feisty and Gutsy.
June 28th, 2007: v3c: Updated patch and debs for the new Rhythmbox release.
August 16th, 2007: v3d: Updated patch and debs for Rhythmbox 0.11.2.
November 14th, 2007: v3e: Updated patch and debs for Rhythmbox 0.11.3. Add Hardy repository.
November 30th, 2007:Updated gusty and hardy builds. Include fixed Croatian po file from Franko Burolo.
February 7th, 2008: v3f: Updated patch and debs for Rhythmbox 0.11.4. (Thanks to Iain Buchanan for notifying me of the missing patch!)
May 31st, 2008: v3g: Updated patch to apply cleanly to Rhythmbox 0.11.5. (The debs for hardy have been at 0.11.5 for quite a while).
October 15st, 2008: v3h: Updated patch to apply cleanly to Rhythmbox 0.11.6. Ubuntu packages are available for i386, amd64, and lpia now.
October 20st, 2008: v3i: Updated patch to apply cleanly to the real Rhythmbox 0.11.6 release. v3h was for a later version from SVN.
April 24th, 2009: v3j: Update patch to apply cleanly to Rhythmbox 0.12.0. Provide debs for Ubuntu Jaunty.
November 4th, 2009: v3k: Update patch to apply cleanly to Rhythmbox 0.12.5 and provide debs for Ubuntu Karmic.
November 29th, 2009: v3l: Update patch to apply cleanly to Rhythmbox 0.12.6 and provide debs for Ubuntu Lucid too.
April 25th, 2010: v3m: Update patch to apply cleanly to Rhythmbox 0.12.8. Provide debs for Ubuntu Lucid.
Jun 3rd, 2010: v3n: Update patch to apply cleanly to Rhythmbox 0.12.8git20100602. Provide debs for Ubuntu Maverick Meerkat 10.10.
Jun 13th, 2010: v3o: Update patch to apply cleanly to Rhythmbox 0.12.8git20100611. Updated debs for Ubuntu Maverick Meerkat 10.10.
October 10th, 2010: v3p: Update patch to apply cleanly to Rhythmbox 0.13.1. Provide updated debs for Ubuntu Maverick Meerkat 10.10.
April 4th, 2011: v3p: Update patch to apply cleanly to Rhythmbox 0.13.3. Provide debs for Ubuntu Natty Narwhal 11.04.
October 16th, 2011: v3r: Updated patch for new plug-in infrastructure in Rhythmbox 2.90.1. Provide debs for Ubuntu Oneiric Ocelot 11.10.
December 23rd, 2011: v3s: Updated patch. Provide debs for Ubuntu Precise Pangolin 12.04.
January 14th, 2012: v3t: Update patch and debs for Ubuntu Precise.
